Cookies Notice
This site uses cookies to deliver services and to analyze traffic.
📣 Guardian Agent: Guard AI-generated code
Open source software (OSS) is the foundation of modern digital infrastructure – but with convenience comes hidden risk.
The average application now pulls in hundreds of third-party dependencies, challenging engineers to validate potential security risks from vulnerabilities. Security teams need more than lists of CVEs. They need context, quality signals, and proactive guardrails to ensure their software supply chain is healthy, reliable, and secure.
Traditional SCA tools focus on delimited vulnerability lists (CVEs). But what happens if…
Today, we are excited to unveil an answer: Apiiro’s new OSS Package Health & Reputation capabilities.
We are expanding our SCA experience to bring rich community signals, operational health data, and proactive governance into overall OSS package risk assessment – so even your most complex third-party dependencies come with the context you need to stay secure.
Relying solely on vulnerability databases is like checking a car’s history report to figure out why the engine is smoking. Applying encyclopedic data to dynamic, dependent applications will always leave security teams on the backfoot.
To truly secure the software supply chain, organizations must look at the intent, activity, and quality behind packages.
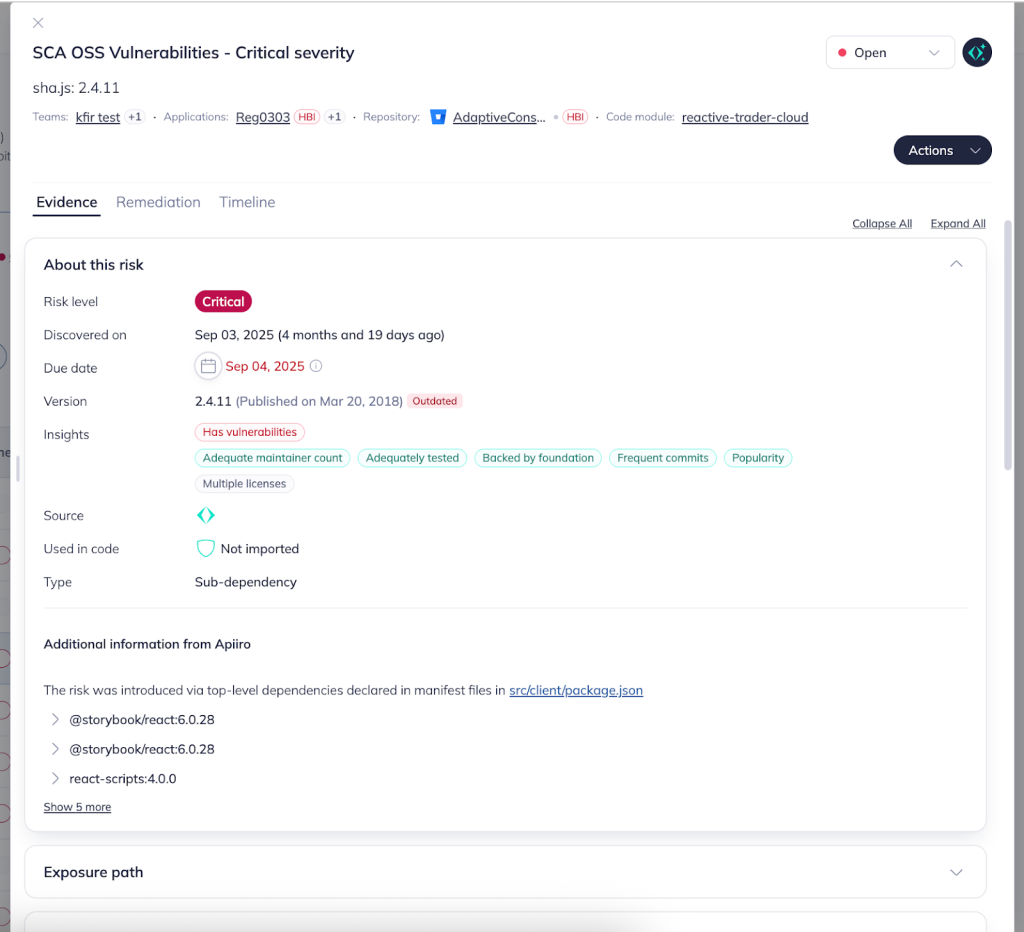
Most “hidden” supply chain risks fall into three categories that CVEs simply don’t capture:
Abandonment: Stale packages that no longer receive security patches.
Low Trust: Packages with no community backing or transparent ownership.
Malicious Volatility: New or “typosquatted” packages that haven’t yet been flagged as malicious, but exhibit high-risk behavior.
🚨 Poor package health can slow remediation, introduce fragile dependencies, and expose organizations to operational instability and supply chain threats.
Apiiro’s new OSS insights bring reputation and popularity metrics, and operational health indicators, into your AppSec workflows – so you can manage risk from the package-level up – not just when an issue appears in a database.
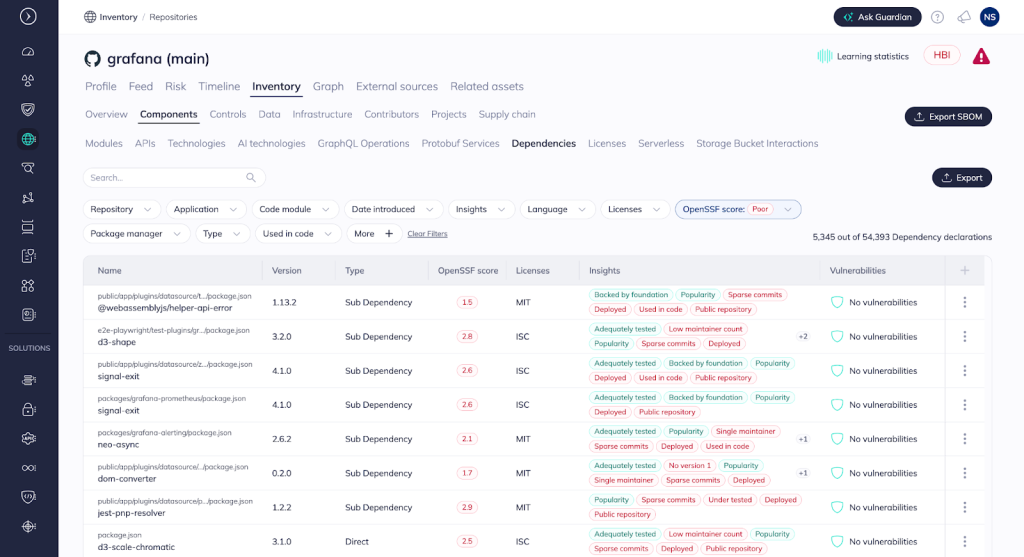
These insights go well beyond rote lists of CVEs, offering intelligent, multi-faceted reliability and risk signals:
By combining these signals, teams can gain a nuanced view of a package’s standing, helping to spot risky, fringe, or low-trust dependencies long before they reach production.
Insights are only valuable if they lead to action. Apiiro starts from the moment a new package version is deployed, with the cooldown period policy. Going forward, by continuously and seamlessly integrating health signals into the Apiiro Policy Engine, teams can also automate guardrails across the entire SDLC.
One of the most powerful new capabilities is the ability to enforce a cooldown period (e.g., 72 hours) on new package versions.
💡 Why a cooldown? Research shows that the majority of malicious or “poisoned” packages are identified and pulled from registries within the first 48 hours. By preventing the immediate adoption of “bleeding-edge” releases, you create a vital safety buffer that lets the global security community vet the code before it reaches your production environment.
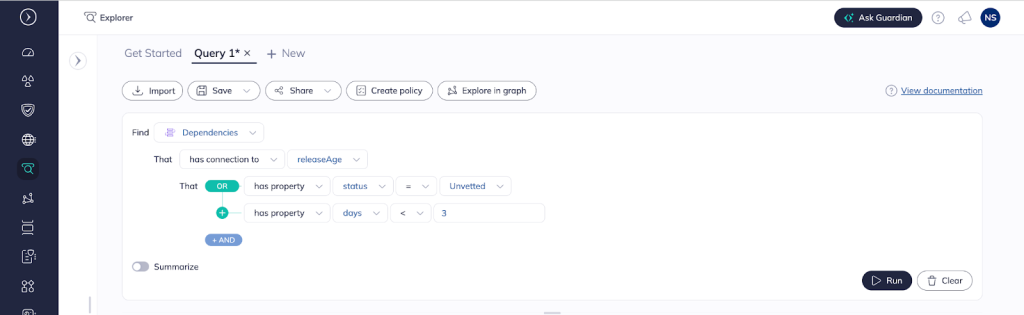
Two powerful automation capabilities focus on keeping the SDLC secure against low-reputation and stale packages:
With package health and reputation insights integrated into your existing security posture management, you can:
The democratization of open source software has made nuance and context nearly impossible. But Apiiro enables development teams to leverage the immense capabilities of open source digital infrastructure, without endangering their SDLCs.
By combining reputation metrics, health indicators, and powerful policy automation, teams can move from reactive SCA to proactive package governance, elevating their security posture while improving development velocity.
See how Apiiro secures your SDLC against OSS sprawl. 👉 Get a demo.