Cookies Notice
This site uses cookies to deliver services and to analyze traffic.
📣 Guardian Agent: Guard AI-generated code
Unified risk and vulnerability management across application, infrastructure, and code quality scanners, with code-to-runtime actionable context
Automated security controls validation and assurance based on your organization’s SDLC policies, with actionable context from your CMDB
Risk Graph policy engine and developer’s guardrails at every phase: design, development (pull request), and delivery (build/deploy)



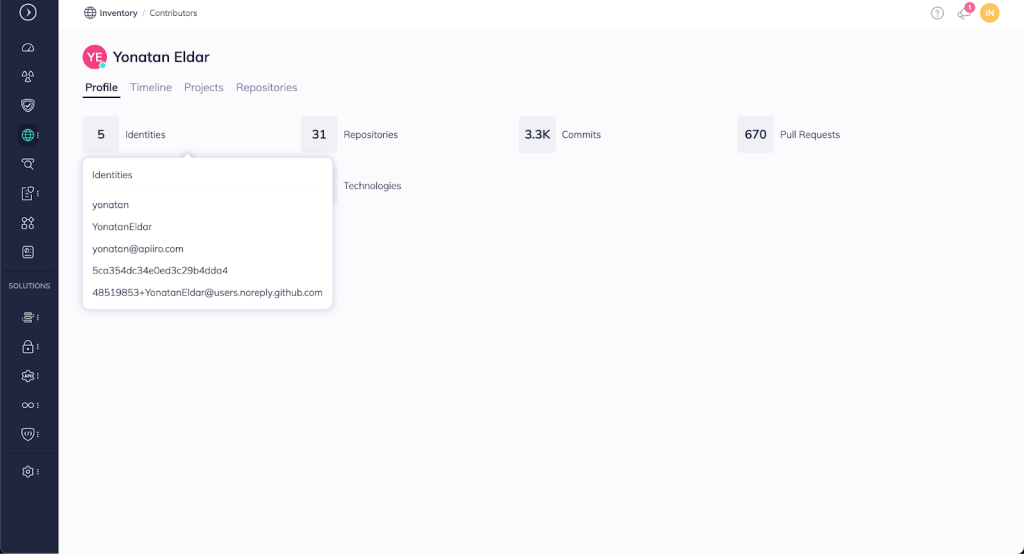
Managing identities across diverse systems is a daunting challenge, even for experienced application security experts. Practitioners need a reliable method to track and secure all user activities within their applications, especially when multiple systems are in play. Apiiro addresses this challenge with its powerful identity matching algorithm, which integrates data from various sources to provide a single, holistic view of application security.
Identity matching is crucial for several reasons: it enables accurate identification of code owners, helps automate remediation processes, and ensures that only the right people have access to sensitive areas of the codebase. However, traditional methods of identity matching are often error-prone, leading to inefficiencies and increased security risks.
Apiiro’s identity matching algorithm addresses these challenges by offering a robust, scalable solution that integrates with various systems to provide a comprehensive overview of all identities involved in application development and security. This capability not only improves security posture management but also enhances workflow automation and compliance.
Managing identities across different systems — such as SCM providers, ticketing systems, and identity providers like OKTA—is a significant pain point in application security. Without a reliable system to match identities, security teams struggle – both to pinpoint who is responsible for specific code changes, and to gain visibility into active committers to the codebase. Doubts around who is accessing critical systems and what changes they may have made prevents effective risk management.
Apiiro’s identity matching algorithm is a game-changer for security teams. By seamlessly integrating with SCM providers, ticketing systems, and identity providers, the algorithm allows users to track and manage identities across their entire application ecosystem.
This feature underpins many of Apiiro’s capabilities, enabling users to automate processes that would otherwise be manual and error-prone. For example, identity matching provides benefits across the following areas of application security:
Contributors: Highlights active developers and their contributions, helping security teams monitor ongoing work.
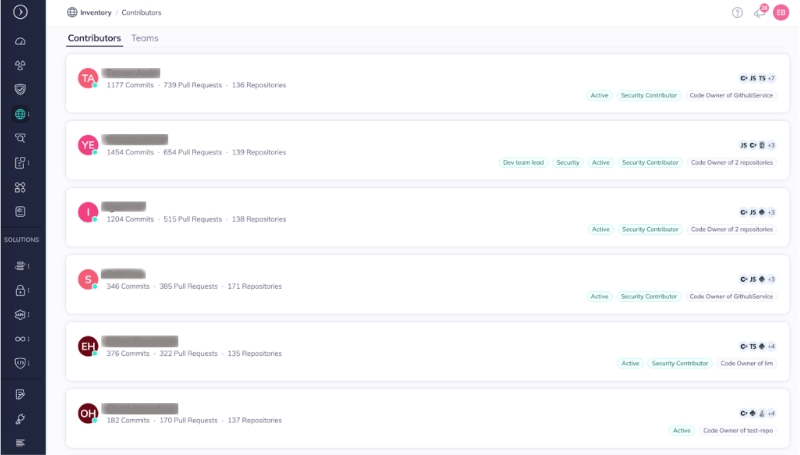
Workflow and Automation: Automates the process of sending tasks to the correct individuals based on identity matching. This can be done via many ticketing and messaging platforms, including Slack, MS Teams, and Jira – all of which are supported by integrations with Apiiro.
Inventory Overview Dashboard: Detects abnormal commits, ensuring only authorized users are making changes.

Licensing Reports: Accurately tracks active contributors and provides visibility to the trend over time of developers who committed code in the last 90 days in the organization. This can help organizations forecast growth and allocate resources accordingly.

Apiiro’s identity matching algorithm is built on advanced graph-based clustering techniques. It represents organizational activity — such as handling tickets, commits, and pull requests — as a network of nodes and edges. This graph structure allows Apiiro to cluster related activities and identities, providing a clear view of who is responsible for what. The scope here is entirely inclusive, as Apiiro’s graph-based clustering occurs across all different providers – SCM, ticketing, identity providers – ensuring coverage of all the possible workflows in your organization where development activity occurs.
A critical aspect of the algorithm is its ability to detect and filter out non-human identities, such as bots and automations, ensuring that only legitimate users are included in security assessments. This reduces noise, improves the accuracy of the security posture analysis, and addresses the validity of your team’s most important resource: people.
Identity matching is a complex but essential aspect of application security, and Apiiro’s algorithm simplifies this process significantly. By providing a unified view of identities across many development systems, it enables security teams to automate workflows, detect potential risks, and ensure compliance with minimal manual intervention.
Key Takeaways:
This site uses cookies to deliver services and to analyze traffic.